
Vasanth

The EU Cyber Resilience Act (CRA) is widely understood as cybersecurity legislation targeting software vulnerabilities and digital product security. However, manufacturers of physical products with digital elements face substantial compliance obligations that extend far beyond IT security teams. The CRA compliance burden encompasses supply chain documentation, product lifecycle management, material traceability, and continuous reporting requirements that intersect with existing regulatory frameworks.
This analysis examines the operational and documentation challenges manufacturers face under CRA, focusing on the compliance infrastructure required to maintain market access. Understanding how CRA obligations interact with REACH, RoHS, and other product compliance frameworks helps manufacturers avoid fragmented compliance approaches that increase cost and risk.
Table of Contents
Why CRA Creates Broader Compliance Obligations Than Cybersecurity Alone
CRA Scope: Which Products and Manufacturers Are Covered
Documentation Requirements Beyond Security Patches
Supply Chain Transparency and Component Traceability Under CRA
How CRA Intersects with Existing Product Compliance Frameworks
Enforcement Timeline and Compliance Deadlines
Operational Impact on Manufacturing and Product Development
Strategic Compliance Infrastructure for CRA Readiness
How AI-Native Compliance Automation Addresses CRA Complexity
Frequently Asked Questions
Conclusion
Why CRA Creates Broader Compliance Obligations Than Cybersecurity Alone
The EU Cyber Resilience Act establishes cybersecurity requirements for products with digital elements placed on the EU market. While security vulnerabilities and patch management receive primary attention, the regulation imposes documentation, traceability, and reporting obligations that affect manufacturing operations, supply chain management, and product compliance infrastructure.
CRA compliance burden extends to manufacturers who never considered themselves software companies. Industrial automation equipment, medical devices, automotive components, and energy storage systems with embedded firmware or network connectivity fall under CRA scope.
The operational challenge emerges from CRA's lifecycle approach. Compliance does not end at product placement—manufacturers must maintain vulnerability monitoring, issue security updates, and document all modifications throughout the product's supported lifetime. This creates continuous documentation obligations similar to post-market surveillance under medical device regulations or WEEE reporting requirements.
CRA documentation requirements parallel existing product compliance frameworks in structure and complexity. Manufacturers already maintaining continuous audit-ready documentation for REACH, RoHS, and conflict minerals face similar challenges with CRA: version control, supplier data collection, component traceability, and multi-framework reporting.
CRA Scope: Which Products and Manufacturers Are Covered
Understanding which products trigger CRA obligations determines resource allocation and compliance strategy. The regulation applies to products with digital elements, defined broadly to include hardware and software components that process, store, or transmit data.
Covered Product Categories
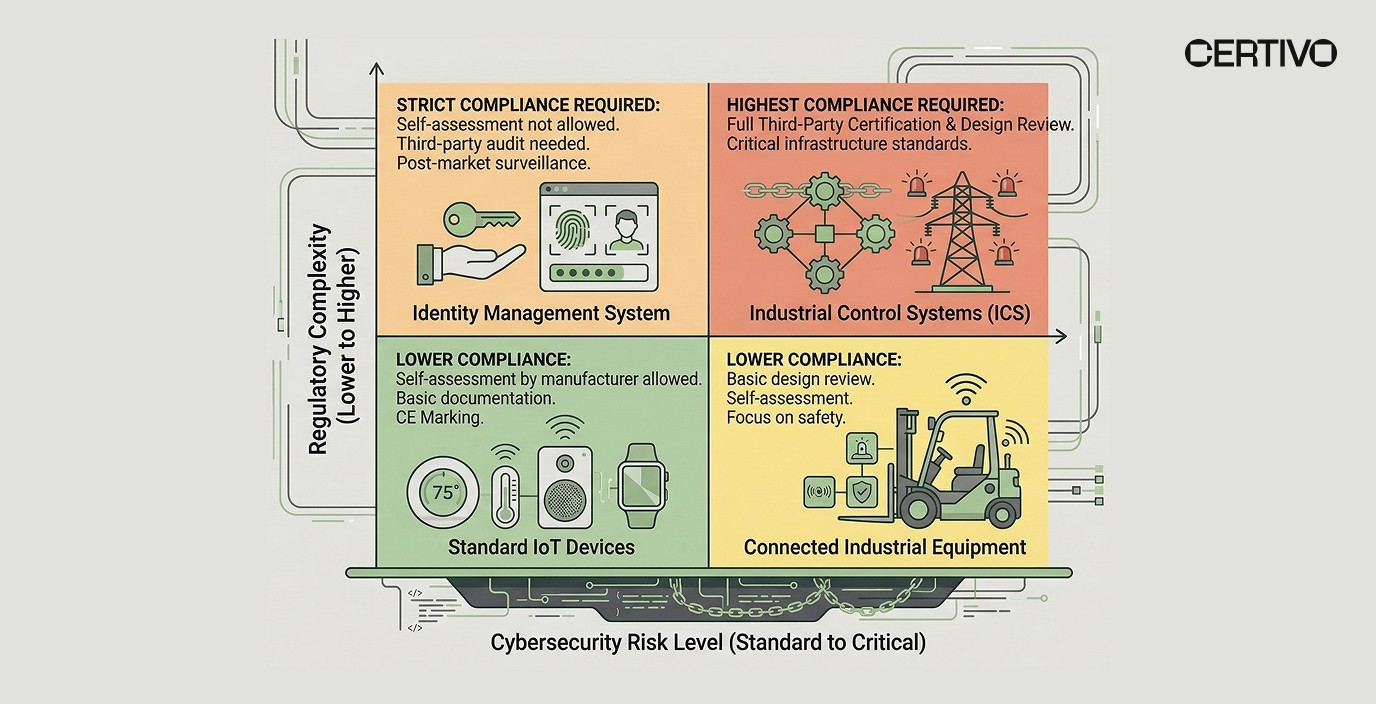
Critical Products with Digital Elements: Products in Annex III face stricter requirements, including third-party conformity assessment. Categories include identity management systems, network management tools, and security-critical industrial control systems.
Standard Products with Digital Elements: Most manufacturers fall into this category, covering products with embedded software, network connectivity, or data processing capabilities. Examples include connected industrial equipment, smart sensors, building automation systems, and IoT devices.
Software Products: Standalone software and cloud services with security implications, including operating systems, database management systems, and enterprise software with privileged access.
Exclusions and Exemptions
Medical devices regulated under MDR/IVDR face modified CRA requirements to avoid regulatory overlap. Aviation and automotive products under sector-specific safety regulations may have exemptions for certain provisions. However, manufacturers cannot assume automatic exclusion—legal analysis determines applicability.
Open-source software contributors face limited obligations under certain conditions, but manufacturers incorporating open-source components into commercial products retain full CRA responsibility.
Manufacturer vs. Importer Obligations
EU-established manufacturers bear primary responsibility for CRA compliance, including conformity assessment, technical documentation, and CE marking. Importers placing products from non-EU manufacturers assume equivalent obligations if the manufacturer does not designate an authorized representative.
Expanding into EU markets requires understanding these role definitions and establishing appropriate legal relationships with importers and distributors.
Documentation Requirements Beyond Security Patches
CRA mandates comprehensive technical documentation that extends far beyond vulnerability management procedures. Manufacturers must maintain detailed records covering design specifications, risk assessments, security testing, and supply chain composition.
Technical Documentation Components
Design and Development Documentation: Complete description of product architecture, security features, data flows, and system boundaries. Documentation must explain security-by-design principles and how cybersecurity requirements were integrated throughout development.
Risk Assessment Records: Systematic identification of cybersecurity risks, threat modeling results, and mitigation measures. Risk assessments must address the entire product lifecycle, including deployment, operation, maintenance, and decommissioning.
Component and Dependency Mapping: Detailed inventory of all software components, libraries, dependencies, and third-party elements. This parallels BOM-level compliance intelligence requirements under REACH and RoHS, extending the concept to software dependencies and firmware components.
Security Testing Evidence: Results from penetration testing, vulnerability scanning, code analysis, and security audits. Documentation must demonstrate compliance with essential cybersecurity requirements throughout testing phases.
Supply Chain Security Documentation: Evidence of supplier security assessments, component provenance verification, and supply chain risk management procedures. Manufacturers must document how they ensure third-party components meet CRA requirements.
Continuous Documentation Obligations
Unlike one-time conformity assessments, CRA requires ongoing documentation updates. When vulnerabilities are discovered, patches deployed, or components updated, manufacturers must document changes and maintain complete version history.
This creates documentation burden similar to medical device compliance post-market surveillance, where manufacturers track field performance, incidents, and corrective actions throughout product lifetime.
Continuous audit-ready documentation systems that manufacturers use for substance compliance, conflict minerals, and WEEE reporting provide relevant operational models for CRA documentation management.
Supply Chain Transparency and Component Traceability Under CRA
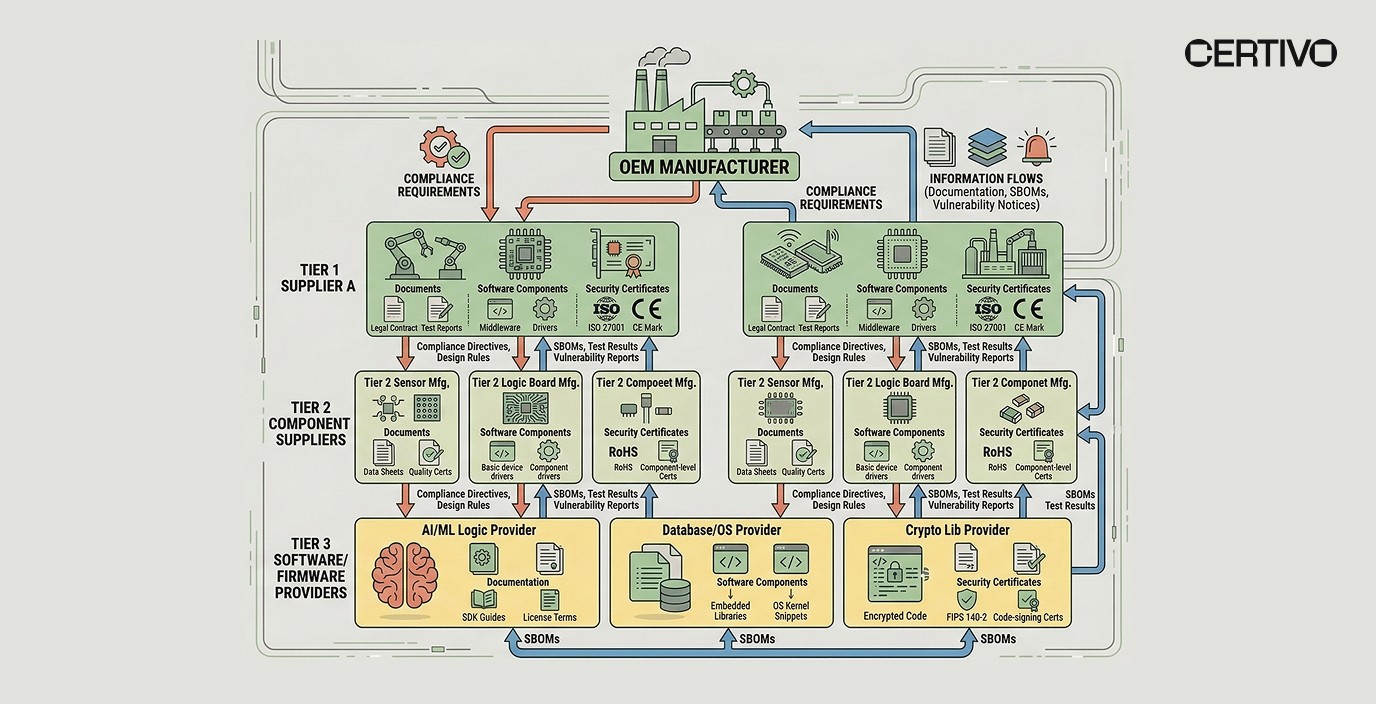
CRA's supply chain requirements create compliance burden extending deep into supplier networks. Manufacturers must verify that components, libraries, and software dependencies meet essential cybersecurity requirements, document supplier security practices, and maintain traceability throughout product lifecycle.
Supply Chain Security Assessment
Manufacturers cannot simply accept supplier declarations of CRA compliance. The regulation requires evidence-based verification of supplier security practices, component vulnerability management, and incident response capabilities.
This parallels existing supplier risk scoring and ESG ratings processes that manufacturers use for conflict minerals due diligence and supplier quality management. CRA adds cybersecurity verification to existing supplier assessment frameworks.
Component Provenance and Traceability
CRA requires manufacturers to identify and document all software components, including open-source libraries, commercial software, and custom code. When vulnerabilities are discovered in any component, manufacturers must rapidly identify affected products and deploy patches.
Without BOM-level substance intelligence extended to software components, manufacturers cannot meet CRA traceability requirements at scale. The same infrastructure that tracks restricted substances in material declarations must now track software dependencies across product portfolios.
Multi-Tier Supply Chain Visibility
Components may contain nested dependencies—commercial software incorporating open-source libraries, firmware using third-party modules, and hardware with embedded software from component manufacturers. Multi-tier supply chain transparency becomes essential for CRA compliance.
Manufacturers must establish supplier self-service compliance portals that collect not just material declarations and test reports, but also software bills of materials (SBOMs), vulnerability disclosure procedures, and security patch commitments.
How CRA Intersects with Existing Product Compliance Frameworks
Manufacturers already navigate complex regulatory landscapes combining REACH, RoHS, WEEE, conflict minerals, and industry-specific requirements. CRA adds another framework requiring integrated compliance infrastructure rather than siloed management.
Operational Parallels with Product Compliance
Documentation Lifecycle Management: CRA technical documentation requirements mirror REACH technical dossiers and RoHS technical documentation. Both require design specifications, risk assessments, testing evidence, and supplier data maintained throughout product lifetime.
Supply Chain Data Collection: CRA supplier security assessments follow similar patterns to conflict minerals due diligence and REACH substance declarations. Manufacturers need standardized supplier questionnaire frameworks covering both material composition and cybersecurity practices.
Component-Level Traceability: Just as BOM-level material mapping tracks restricted substances in components, CRA requires software component tracking with version control and vulnerability status. The data structures and traceability systems overlap significantly.
Continuous Monitoring Requirements: Regulatory intelligence and horizon scanning for REACH SVHC additions, PFAS restrictions, and RoHS exemption sunsets extends naturally to CRA vulnerability databases and security advisories.
Integration with Digital Product Passports
The EU Digital Product Passport initiative under the Ecodesign for Sustainable Products Regulation (ESPR) creates another intersection point. Digital passports must contain product composition, repair information, and environmental data—CRA adds cybersecurity information to the same infrastructure.
Manufacturers implementing digital passports and traceability IDs for battery regulations and circular economy requirements can extend these systems to CRA compliance data rather than building parallel infrastructure.
Coordinating Cross-Functional Compliance Teams
CRA compliance cannot sit solely within IT security departments. Engineering teams managing design-for-compliance PLM workflows must incorporate cybersecurity requirements alongside restricted substance avoidance. Procurement teams managing supplier compliance for materials must add cybersecurity verification to existing processes.
Integrated PLM and ERP compliance systems provide the infrastructure to coordinate these cross-functional requirements without creating data silos or duplicative processes.
Enforcement Timeline and Compliance Deadlines
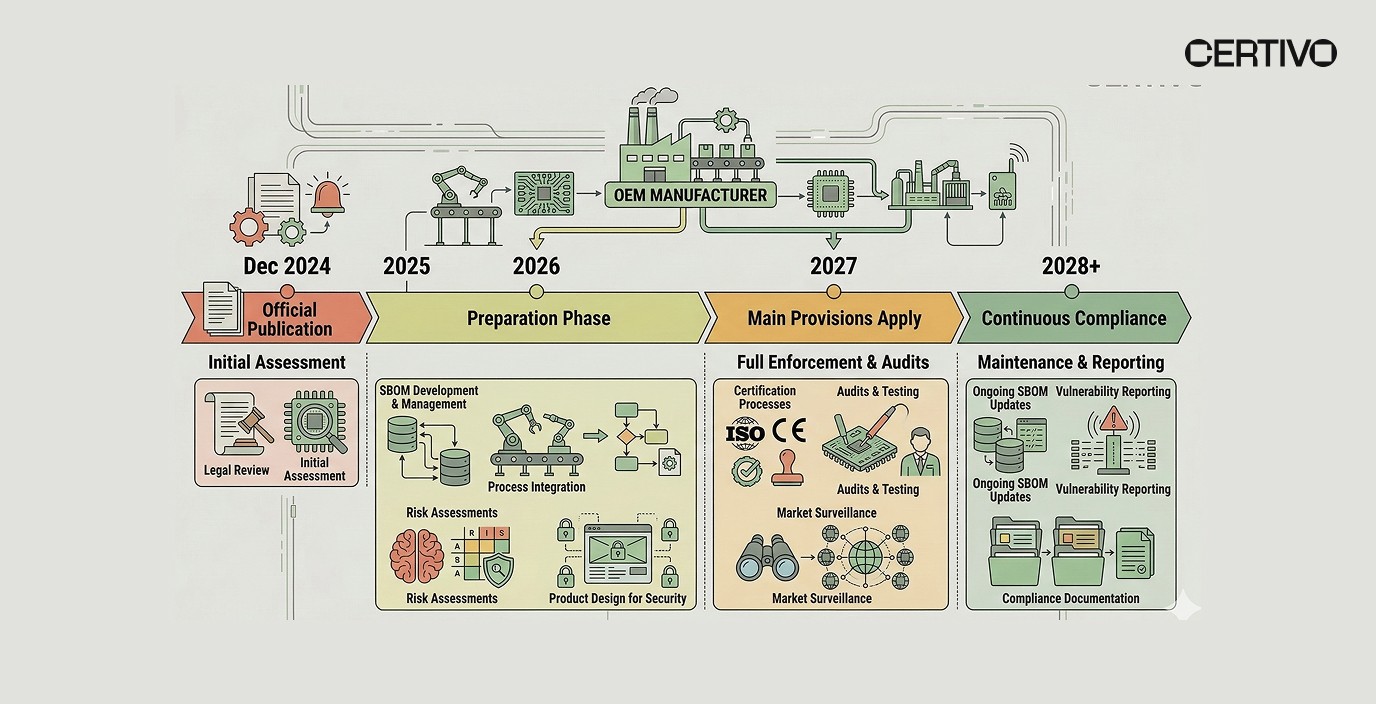
Understanding CRA implementation timeline determines resource allocation and preparation priorities. The regulation follows a phased enforcement approach with different obligations activating at different dates.
Key Milestone Dates
December 2024: CRA formally adopted and published in Official Journal. Member states have transposition period to incorporate into national law.
2027: Main CRA provisions become applicable. Manufacturers must meet essential cybersecurity requirements, complete conformity assessments, and apply CE marking for newly placed products.
Critical and Important Product Categories: Products in Annex III face stricter timelines and third-party conformity assessment requirements. Manufacturers should identify whether products fall into these categories immediately.
Existing Products in Market: Products already placed on market before applicability dates are not automatically subject to CRA retroactively. However, manufacturers maintaining these products must still address newly discovered vulnerabilities and may need to implement security updates to maintain market access.
Preparation Timeline Recommendations
Immediate Actions (2025-2026):
Conduct gap analysis identifying which products fall under CRA scope
Map current cybersecurity practices against essential requirements
Assess technical documentation completeness and identify gaps
Begin supplier compliance verification for software components and security practices
Near-Term Actions (2026-2027):
Complete conformity assessments for products in development
Establish vulnerability monitoring and patch management procedures
Implement component traceability systems linking software dependencies to products
Train engineering and compliance teams on CRA requirements
Continuous Obligations (2027+):
Maintain technical documentation with version control
Monitor vulnerability databases and security advisories
Deploy security updates throughout product supported lifetime
Report actively exploited vulnerabilities to ENISA within 24 hours
The EU CRA enforcement timeline provides detailed analysis of these deadlines and their operational implications.
Operational Impact on Manufacturing and Product Development
CRA compliance burden affects manufacturing operations, product development cycles, and go-to-market timelines. Understanding these operational impacts helps organizations allocate resources and adjust processes.
Product Development Process Changes
Design Phase: Engineers must incorporate security-by-design principles from initial concept development. This parallels design-for-compliance PLM workflows that flag restricted substances during material selection—CRA extends this to software architecture and component selection.
Component Selection: Procurement decisions must now include cybersecurity verification alongside technical specifications, cost, and availability. Selecting components with unknown security practices or poor vulnerability management creates downstream compliance risk.
Testing and Validation: Security testing becomes a formal stage gate requirement, not an optional verification. Penetration testing, vulnerability scanning, and security code review must be completed and documented before product release.
Documentation Requirements: Technical file preparation extends beyond traditional product specifications to include risk assessments, security testing results, and supplier security documentation. This increases documentation burden per product.
Supply Chain Management Complexity
Supplier Qualification: Existing supplier qualification processes covering quality, delivery, and material compliance must now include cybersecurity assessment. Supplier risk scoring frameworks extend to include security practices and vulnerability response capabilities.
Component Obsolescence Management: When component manufacturers discontinue products or cease security support, CRA-covered manufacturers must either replace components (potentially requiring recertification) or assume security maintenance responsibility.
Change Management: Component substitutions, software updates, and design modifications require assessment of CRA compliance impact. This adds complexity to existing engineering change order (ECO) processes.
Post-Market Obligations
Vulnerability Monitoring: Manufacturers must continuously monitor for newly discovered vulnerabilities in their products and all incorporated components. This requires ongoing resources beyond traditional product support.
Patch Development and Deployment: When vulnerabilities are identified, manufacturers must develop, test, and deploy security patches. For products with constrained connectivity or deployed in sensitive environments, patch deployment poses operational challenges.
Incident Reporting: Actively exploited vulnerabilities must be reported to ENISA within 24 hours. This requires incident detection capabilities, classification procedures, and established reporting workflows.
The operational impact resembles post-market surveillance requirements for medical devices, where manufacturers maintain continuous monitoring and reporting obligations throughout product lifetime.
Strategic Compliance Infrastructure for CRA Readiness
Organizations approaching CRA as isolated cybersecurity regulation miss opportunities to leverage existing compliance infrastructure. Strategic readiness integrates CRA obligations into enterprise compliance frameworks covering product safety, substance restrictions, and supply chain verification.
Unified Compliance Data Management
Centralized Documentation Repository: Technical files for CRA, REACH dossiers, RoHS technical documentation, and conflict minerals reports share common elements—product specifications, BOMs, supplier data, test results. Centralized compliance data management eliminates duplicate data entry and version control issues.
Component-Level Traceability: Extending BOM-level compliance intelligence to include software components, firmware versions, and security patch status creates unified traceability infrastructure supporting both material compliance and CRA obligations.
Supplier Data Integration: Supplier self-service portals collecting material declarations, test reports, and conflict minerals data expand to include SBOMs, vulnerability disclosure procedures, and security certifications—using the same collection infrastructure and validation workflows.
Cross-Framework Regulatory Monitoring
Horizon Scanning Automation: Organizations monitoring REACH SVHC additions, PFAS restrictions, and RoHS exemption sunsets extend regulatory intelligence and horizon scanning to CRA vulnerability databases, security advisories, and enforcement guidance.
Impact Assessment Workflows: When regulations change—new REACH restrictions, updated RoHS exemptions, or CRA implementation guidance—manufacturers need systematic processes to identify affected products and assess compliance impact across frameworks simultaneously.
Product Lifecycle Compliance Integration
Stage Gate Compliance Checks: Integrated PLM and ERP compliance embeds both material compliance and CRA security requirements into product development stage gates, preventing non-compliant products from reaching production.
Change Management Processes: Engineering change orders trigger automated compliance impact assessment across material restrictions, security requirements, regulatory documentation, and customer notifications—treating compliance holistically rather than in functional silos.
Customer-Facing Compliance Transparency: Customer trust centers providing material declarations, compliance certificates, and test reports expand to include CRA conformity documentation and security update information—using unified disclosure infrastructure.
How AI-Native Compliance Automation Addresses CRA Complexity
Manual compliance management cannot scale across expanding regulatory frameworks, complex supply chains, and continuous monitoring obligations. AI-native compliance automation reduces CRA compliance burden while improving documentation accuracy and response time.
Automated Document Intelligence for CRA
Technical Documentation Assembly: AI systems extract relevant data from design specifications, test reports, risk assessments, and supplier documentation to automatically assemble CRA technical files. This parallels automated regulatory dossier generation for REACH registration and other regulatory submissions.
SBOM Analysis and Component Tracking: AI analyzes software bills of materials to identify all components, dependencies, and versions across product portfolios. When vulnerabilities are discovered in any component, CORA-driven compliance intelligence immediately identifies all affected products.
Supplier Security Assessment: AI processes supplier security questionnaires, certifications, and vulnerability management procedures to generate supplier risk scores combining cybersecurity practices with existing quality, delivery, and compliance metrics.
CORA-Powered Vulnerability Monitoring
Continuous Threat Intelligence: CORA intelligence monitors vulnerability databases, security advisories, and threat intelligence feeds across all components and dependencies in manufacturer product portfolios. This automated monitoring replaces manual scanning of multiple databases and bulletin boards.
Impact Assessment Automation: When new vulnerabilities are disclosed, CORA-enabled analysis automatically identifies affected products, assesses severity based on deployment context, and prioritizes remediation based on exploitation risk and regulatory reporting obligations.
Regulatory Reporting Automation: For vulnerabilities meeting ENISA reporting thresholds, AI systems assemble required information, generate structured reports, and submit through appropriate channels—ensuring 24-hour reporting deadlines are met.
Cross-Framework Compliance Orchestration
Unified Compliance Dashboards: AI aggregates compliance status across CRA, REACH, RoHS, conflict minerals, and other frameworks into real-time SKU compliance dashboards showing which products meet requirements for which markets.
Predictive Compliance Gap Analysis: CORA's regulatory intelligence layer analyzes upcoming regulatory changes across frameworks—new REACH restrictions, CRA implementation guidance, PFAS bans—and predicts compliance gaps before enforcement begins, enabling proactive remediation.
Documentation Version Control: AI maintains complete audit trails across all compliance documentation, tracking changes to technical files, supplier data, test reports, and regulatory submissions across multiple frameworks with unified version control.
The AI compliance transformation reduces CRA compliance burden from overwhelming operational challenge to manageable, systematic process integrated with existing regulatory obligations.
Frequently Asked Questions
Does CRA apply to products already on the market before 2027?
Products placed on the EU market before CRA applicability dates generally do not require retroactive conformity assessment. However, manufacturers must still address newly discovered vulnerabilities in these products and may need to provide security updates to maintain customer trust and contractual obligations. Products undergoing substantial modification after 2027 may be considered new placements requiring full CRA compliance.
How does CRA interact with existing product safety regulations?
CRA complements rather than replaces existing product safety frameworks. Medical devices continue following MDR/IVDR with modified CRA requirements. Automotive and aerospace products under sector-specific regulations may have partial exemptions. Manufacturers must conduct legal analysis to understand how CRA obligations interact with applicable sector regulations and coordinate compliance across frameworks.
What level of supply chain visibility does CRA require?
CRA requires manufacturers to document and verify security practices of suppliers providing components with digital elements. This extends beyond first-tier suppliers to include nested dependencies—open-source libraries in commercial software, firmware in components, and embedded software from sub-suppliers. Multi-tier supply chain transparency becomes essential, requiring structured supplier data collection similar to conflict minerals due diligence.
How long must manufacturers support products with security updates under CRA?
CRA requires security support for the product's expected lifetime or minimum five years from market placement, whichever is longer. Manufacturers must clearly communicate security support periods to customers. When security support ends, manufacturers should provide clear notice and migration guidance. This creates long-term resource commitments for vulnerability monitoring and patch development extending years beyond initial product sale.
Can manufacturers use AI compliance automation to meet CRA documentation requirements?
Yes. AI systems can automate technical documentation assembly, component tracking, vulnerability monitoring, and regulatory reporting—provided the underlying data is accurate and systems maintain audit trails. CORA-powered regulatory intelligence provides the automated monitoring, impact assessment, and reporting capabilities needed to manage CRA obligations at scale. However, manufacturers retain ultimate responsibility for compliance accuracy and must validate AI-generated outputs before submission.
How does CRA compliance burden compare to REACH or RoHS compliance?
CRA compliance burden resembles REACH and RoHS in structure: detailed technical documentation, component-level traceability, supplier verification, and continuous monitoring obligations. The primary difference is CRA's post-market requirements for ongoing vulnerability monitoring and security updates throughout product lifetime. Organizations with mature compliance infrastructure for material restrictions can extend these systems to CRA obligations rather than building separate processes.
Conclusion
The CRA compliance burden extends far beyond cybersecurity patches and IT security procedures. Manufacturers face comprehensive documentation requirements, supply chain transparency obligations, component traceability mandates, and continuous monitoring responsibilities that intersect with existing product compliance frameworks.
Organizations treating CRA as isolated cybersecurity regulation miss opportunities to leverage infrastructure developed for REACH, RoHS, conflict minerals, and other compliance obligations. Strategic readiness integrates CRA into enterprise compliance systems using unified data management, cross-framework monitoring, and AI-native compliance automation.
The operational challenges manufacturers face—supplier data collection, component-level traceability, version control, continuous monitoring, and multi-framework reporting—mirror existing product compliance burdens. AI-driven compliance platforms that reduce PFAS reporting burden, automate REACH declarations, and manage conflict minerals due diligence apply the same capabilities to CRA obligations.
Manufacturers preparing for 2027 enforcement must begin now: conducting gap analysis, establishing supplier verification processes, implementing component traceability systems, and integrating CRA requirements into product development workflows. Organizations leveraging existing compliance infrastructure and AI-native automation transform CRA from overwhelming burden to manageable extension of systematic regulatory readiness. Explore how Certivo supports integrated compliance readiness across CRA, product safety, and substance restrictions.
Vasanth
Vasanth is a skilled Compliance Engineer with over five years of experience specializing in global environmental regulations, including REACH, RoHS, Proposition 65, POPs, TSCA, PFAS, CMRT, EMRT, FMD, and IMDS. With a strong academic foundation in Chemical Engineering from Anna University, he brings a deep technical understanding to compliance processes across complex product lines.
Vasanth excels in analyzing Bills of Materials (BOMs), evaluating supplier declarations, and ensuring regulatory conformity through meticulous review and risk assessment. He is highly proficient in supplier engagement, adept at interpreting material disclosures, and experienced in preparing customer-ready compliance documentation tailored to diverse global standards.
Known for his attention to detail, up-to-date regulatory knowledge, and proactive communication style, Vasanth plays a critical role in maintaining product compliance and advancing sustainability goals within fast-paced, globally integrated manufacturing environments.