
Vasanth

The European Union's Cyber Resilience Act (CRA) introduces mandatory cybersecurity requirements for manufacturers of products with digital elements. With enforcement beginning in 2027, global manufacturers face a critical window to establish EU Cyber Resilience Act compliance infrastructure that spans product design, supply chain transparency, vulnerability management, and continuous documentation.
Unlike traditional product safety regulations, the CRA mandates ongoing cybersecurity obligations throughout a product's lifecycle. Manufacturers must implement secure development processes, maintain vulnerability databases, report incidents to authorities, and provide transparent technical documentation across distributed supply chains. For enterprises managing thousands of SKUs and multi-tier supplier networks, cybersecurity and digital compliance at this scale cannot be executed through spreadsheets or manual tracking systems.
This guide explains how Certivo automates CRA compliance preparation through AI-Native Compliance Automation, BOM-level intelligence, and Centralized Supplier Self-Service Portals that transform cybersecurity documentation from a reactive audit task into continuous operational readiness.
Table of Contents
Why EU Cyber Resilience Act Compliance Requires Automation
Understanding the CRA's Lifecycle Compliance Model
Product Categories and Classification Under the CRA
Technical Documentation and Reporting Obligations
Supply Chain Transparency Challenges in CRA Compliance
Vulnerability Management and Incident Reporting Requirements
How Certivo Automates CRA Compliance Preparation
Regulatory Timeline and Enforcement Milestones
Strategic Compliance Preparation Framework
Frequently Asked Questions
Why EU Cyber Resilience Act Compliance Requires Automation
The CRA represents a fundamental shift from perimeter-based cybersecurity to product-embedded security obligations that extend across the entire manufacturing lifecycle. Manufacturers must now manage cybersecurity compliance at the same granularity as materials and environmental compliance, tracking vulnerabilities, software components, and security attestations at the SKU and BOM level.
Manual compliance systems fail under CRA requirements for three structural reasons:
✓ Lifecycle Duration – Security obligations extend 5+ years post-manufacture
✓ Supplier Depth – Multi-tier supply chains require security documentation from component vendors
✓ Reporting Velocity – Actively exploited vulnerabilities must be reported within 24 hours
For manufacturers operating across multiple jurisdictions, the CRA introduces cybersecurity documentation requirements that intersect with existing frameworks like REACH, RoHS, and conflict minerals reporting. Managing compliance risk proactively requires infrastructure that consolidates security documentation alongside substance declarations and environmental certifications.
Understanding the CRA's Lifecycle Compliance Model
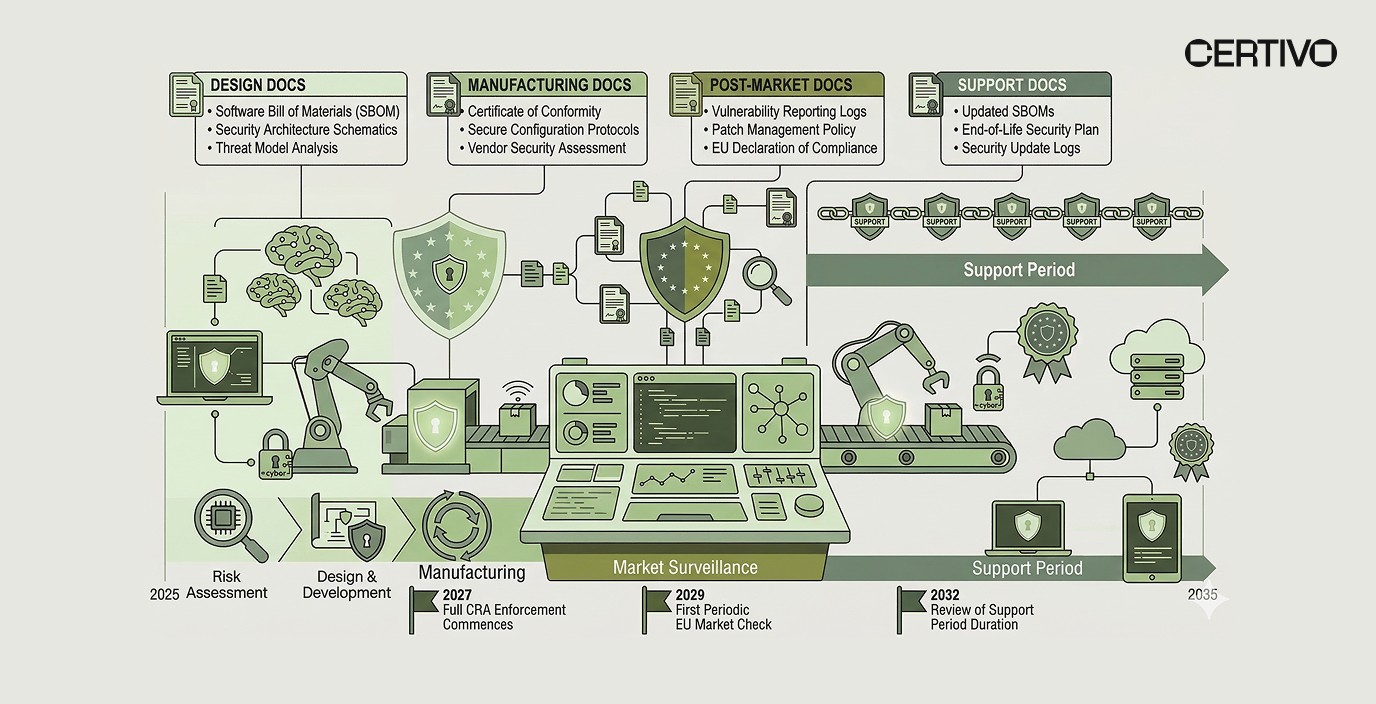
The CRA imposes mandatory security obligations across five distinct lifecycle phases, each generating unique documentation and reporting requirements:
Design Phase Requirements
Manufacturers must implement secure-by-design principles during product development, including threat modeling, security requirements specification, and vulnerability risk assessment. Engineering teams must document security decisions at the component selection stage, creating an audit trail that connects design choices to security outcomes.
Launch new products faster by integrating security documentation directly into PLM workflows through Design-For-Compliance PLM Workflows that capture security requirements during the design phase rather than post-production.
Manufacturing Phase Obligations
Production processes must maintain software bill of materials (SBOM) integrity, verify supplier security attestations, and ensure vulnerability-free components at time of assembly. This requires real-time visibility into component-level security status across multi-tier supply chain transparency networks.
Market Surveillance Period
Post-market obligations include continuous vulnerability monitoring, security update distribution, and incident response coordination. Manufacturers must maintain Continuous Audit-Ready Documentation that proves ongoing security management throughout the product's market presence.
Support and Maintenance Duration
The CRA mandates security support periods proportional to product lifespan, typically 5-10 years for industrial equipment. This creates long-term documentation retention requirements that must survive organizational changes, system migrations, and supplier transitions. Stay audit-ready across frameworks by consolidating CRA documentation with existing compliance records in a unified system.
Product Categories and Classification Under the CRA
The CRA establishes three product classification tiers with escalating compliance obligations. Manufacturers must classify each SKU correctly to determine applicable security requirements and documentation depth.
Important Products (Annex III)
These products undergo conformity assessment by notified bodies before market placement. Categories include:
⚠ Identity Management Systems – Authentication devices, access control hardware
⚠ Network Management Components – Routers, firewalls, VPN appliances
⚠ Operating Systems and Hypervisors – Server OS, virtualization platforms
⚠ Industrial Control Systems – PLCs, SCADA devices, safety controllers
Manufacturers of Important Products must maintain technical documentation demonstrating compliance with security requirements, undergo third-party conformity assessment, and establish post-market surveillance systems. Product safety certification processes must now incorporate cybersecurity verification alongside traditional safety testing.
Critical Products (Article 6)
Critical products pose elevated security risks and require European Cybersecurity Certification Scheme (EUCS) certification. This category includes smart meters, medical devices with network connectivity, and automotive safety systems with remote update capabilities.
Critical product manufacturers face the most stringent documentation requirements, including penetration testing reports, security incident response plans, and continuous vulnerability disclosure procedures.
Standard Products
Products outside Important and Critical categories still face baseline security requirements including vulnerability handling processes, secure default configurations, and transparent technical documentation. Even standard products require systematic compliance tracking when deployed across global supply chains.
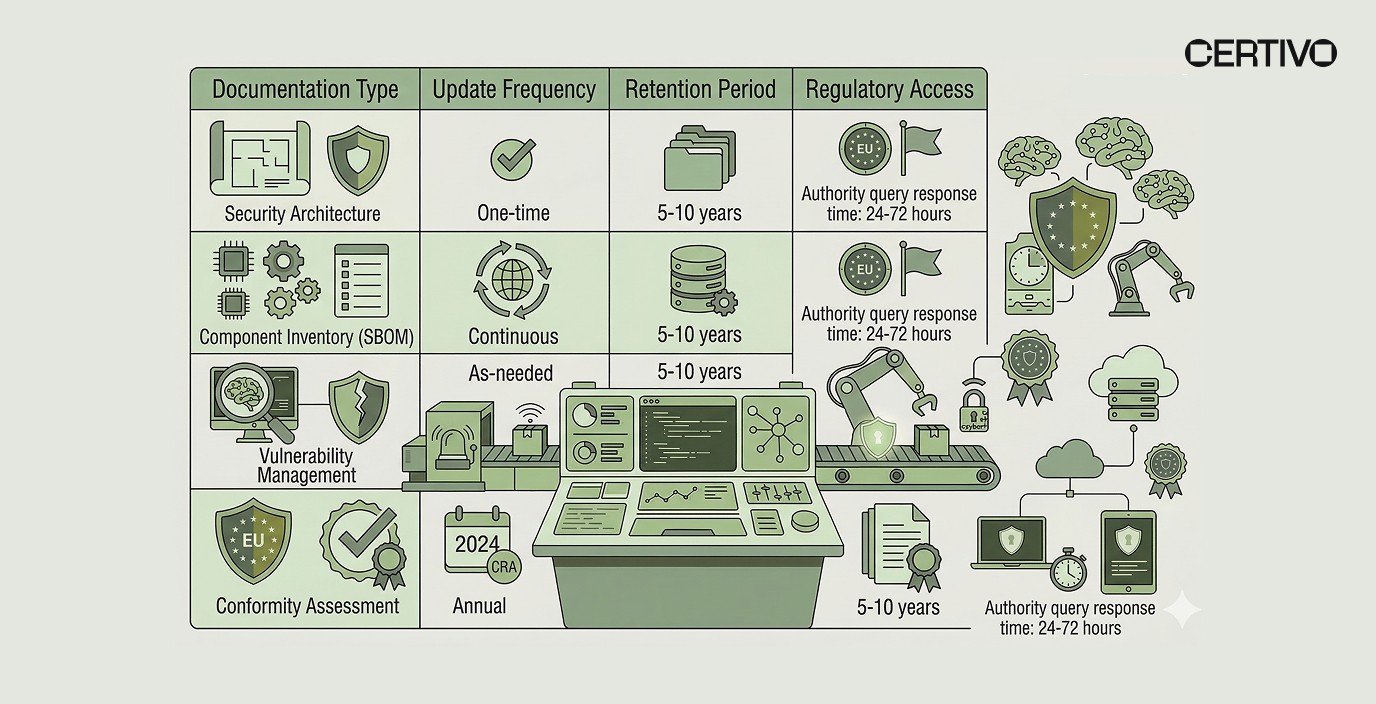
Technical Documentation and Reporting Obligations
CRA compliance generates four categories of technical documentation that must remain accessible throughout product lifecycle:
📊 Security Architecture Documentation – Threat models, security requirements specifications, design decisions
📊 Component Inventory Records – SBOM with version tracking, supplier security attestations
📊 Vulnerability Management Logs – CVE tracking, patch deployment records, incident response documentation
📊 Conformity Assessment Reports – Test results, certification records, notified body attestations
This documentation must be structured to support rapid regulatory queries and market surveillance audits. Traditional document management systems fail because they cannot correlate security documentation with specific SKUs, product versions, or supplier relationships at the granularity CRA enforcement requires.
Replace spreadsheets with a scalable system that maintains version-controlled security documentation linked directly to BOMs and supplier records.
Supply Chain Transparency Challenges in CRA Compliance
The CRA extends security documentation obligations deep into supply chains, requiring manufacturers to collect and verify security attestations from component suppliers who may not directly interface with final product manufacturers.
Multi-Tier Supplier Documentation Requirements
Tier 1 suppliers must provide security declarations for components they integrate. However, those components often contain sub-assemblies from Tier 2 and Tier 3 suppliers who also bear CRA obligations. Manufacturers need Multi-Tier Supply Chain Transparency systems that collect and correlate security documentation across supplier tiers without creating manual data collection bottlenecks.
Traditional supplier portal systems fail because they:
✗ Require manual follow-up for missing documentation
✗ Cannot validate security attestation completeness
✗ Lack version control for updated security declarations
✗ Do not map supplier documentation to specific SKUs or BOM line items
Automated Supplier Data Collection Requirements
Automated Supplier Data Collection & Portals enable suppliers to self-serve security documentation uploads through standardized workflows that validate completeness before submission. Streamline supplier documentation by deploying portals that pre-populate CRA-specific security questionnaires and automatically map responses to affected SKUs.
Certivo's Supplier Self-Service Compliance Portals integrate CORA-powered regulatory intelligence that identifies missing security attestations and automatically generates supplier reminders based on upcoming audit dates or product launch schedules. This transforms supplier data collection from reactive follow-up into proactive compliance preparation. Collaborate with suppliers through portals that reduce documentation collection time from weeks to days.
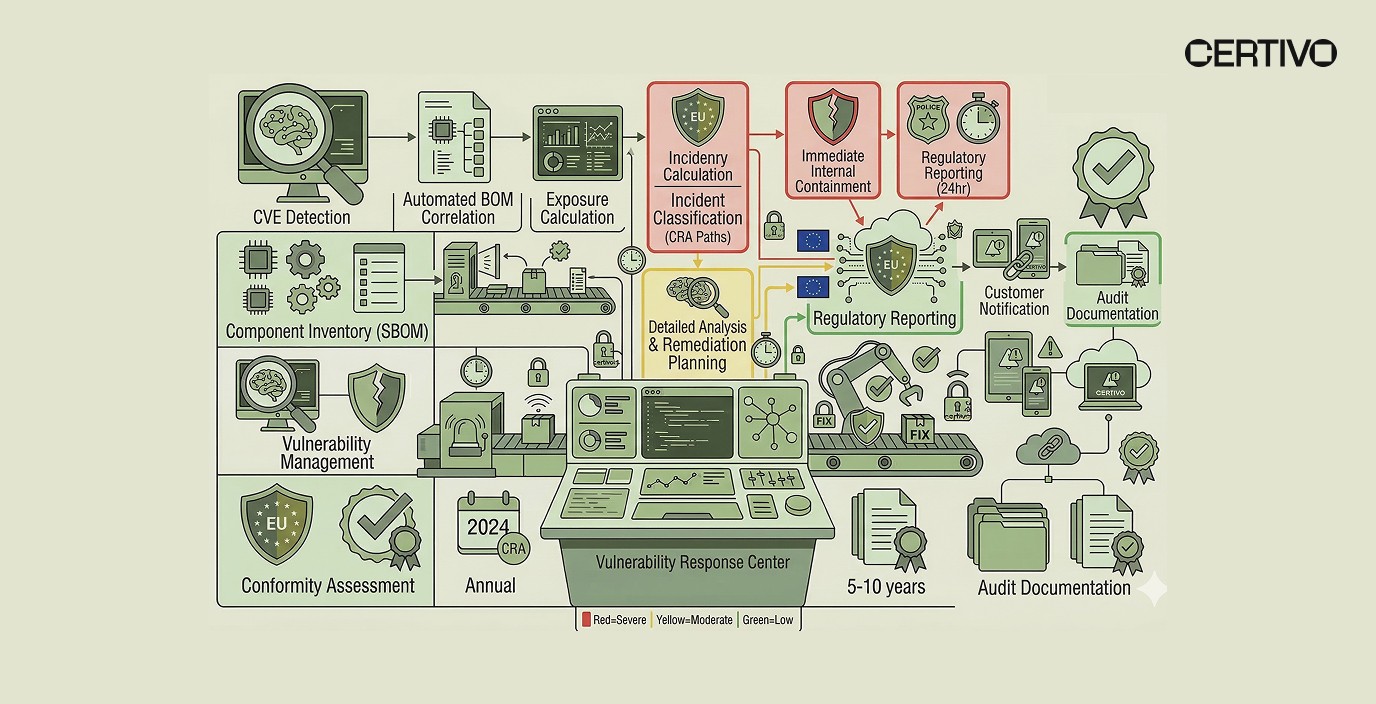
Vulnerability Management and Incident Reporting Requirements
The CRA mandates continuous vulnerability monitoring with strict reporting timelines that escalate based on exploitation status:
⚠ Actively Exploited Vulnerabilities – 24-hour reporting requirement to ENISA
⚠ Severe Vulnerabilities (CVSS ≥ 9.0) – 72-hour incident assessment and mitigation plan
⚠ Moderate Vulnerabilities (CVSS 4.0-8.9) – 30-day remediation timeline
Manufacturers must maintain vulnerability tracking systems that correlate CVE identifiers with specific product versions, deployed SKUs, and affected customer installations. This requires BOM-Level Compliance Intelligence that maps vulnerabilities to component-level data and automatically identifies exposure across product portfolios.
Continuous Compliance Monitoring Infrastructure
Manual vulnerability tracking becomes impossible at scale when manufacturers manage hundreds of product configurations across multiple market regions. Continuous Compliance Monitoring & Audit Readiness systems must:
✓ Ingest CVE feeds and automatically match to BOMs
✓ Calculate vulnerability exposure across product lines
✓ Generate incident reports pre-populated with affected SKUs
✓ Track remediation status through patch deployment records
Certivo automates vulnerability correlation through BOM-Level Material Mapping that links component identifiers to known vulnerability databases and generates exposure reports within minutes of CVE publication. Track compliance by BOM to maintain real-time visibility into security status at component level.
How Certivo Automates CRA Compliance Preparation
Certivo provides the Centralized Compliance Data Backbone required for CRA compliance by integrating security documentation with existing materials compliance, supplier management, and product lifecycle systems.
BOM-Level Security Intelligence
Certivo maintains BOM-Level Compliance Intelligence that tracks security attestations at component level, enabling manufacturers to:
📌 Identify CRA-regulated components within existing product portfolios
📌 Generate product-specific security documentation packages
📌 Correlate supplier security declarations with BOM line items
📌 Track security update deployment across product versions
This eliminates the need for separate cybersecurity tracking systems that duplicate product data and create synchronization challenges between engineering and compliance teams.
CORA-Driven Regulatory Intelligence
CORA's regulatory intelligence layer monitors EU Cyber Resilience Act updates, notified body guidance, and market surveillance enforcement patterns. CORA automatically flags products requiring conformity assessment, identifies documentation gaps, and generates compliance preparation checklists customized to product classification and target markets.
This Regulatory Intelligence & Horizon Scanning capability ensures manufacturers receive advance warning of enforcement milestones and documentation deadlines without manual regulatory monitoring.
Supplier Portal Integration
Certivo's Standardized Supplier Questionnaire Frameworks include CRA-specific security attestation templates that collect:
✓ Component security certifications
✓ Vulnerability disclosure procedures
✓ Software update support commitments
✓ Incident response contact information
Suppliers access portals that display outstanding documentation requests organized by product line and deadline. AI Document Parsing & Certificate Validation automatically extracts security attestation data from uploaded PDFs and validates completeness against CRA requirements. Respond faster to customer RFQs by maintaining audit-ready security documentation that can be packaged and delivered within hours.
Digital Passport Readiness
The CRA intersects with the EU's broader Digital Product Passport requirements, requiring manufacturers to maintain machine-readable product security information accessible throughout product lifecycle. Certivo's Digital Passports & Traceability IDs infrastructure supports CRA compliance by:
📊 Generating unique product identifiers linked to security documentation
📊 Maintaining version-controlled security records accessible via QR codes
📊 Enabling customer self-service access to vulnerability status and update availability
This positions manufacturers for compliance with both CRA security requirements and emerging digital passport mandates under the EU ESPR framework.
Regulatory Timeline and Enforcement Milestones
Understanding CRA enforcement timelines is critical for compliance preparation planning:
2025-2026: Preparation Period
Manufacturers should complete product classification, identify applicable security requirements, and establish Continuous Audit-Ready Documentation infrastructure. This period provides time to standardize compliance across plants and regions before mandatory enforcement begins.
December 2027: CRA Enforcement Begins
All new products placed on EU market must meet CRA requirements. Market surveillance authorities gain enforcement powers including product recalls, market bans, and financial penalties up to €15 million or 2.5% of global annual turnover.
2028-2030: Legacy Product Transition
Existing products remain compliant under pre-CRA rules but face market access restrictions if security vulnerabilities emerge. Manufacturers must decide whether to backport CRA security requirements to legacy products or manage dual compliance frameworks during transition period.
2030+: Full Lifecycle Enforcement
All products in EU market must comply with CRA regardless of manufacture date. This creates long-term documentation retention requirements and ongoing vulnerability management obligations for products manufactured before 2027 enforcement date.
Organizations managing compliance across multiple regulatory frameworks should review how Certivo helps manufacturers prepare for EU Cyber Resilience Act compliance alongside existing materials restrictions and environmental reporting obligations.
Strategic Compliance Preparation Framework
Manufacturers preparing for CRA compliance should execute a phased implementation approach:
Phase 1: Product Classification and Scope Assessment (Q1-Q2 2025)
✓ Classify all SKUs under CRA product categories
✓ Identify Important and Critical products requiring conformity assessment
✓ Calculate documentation requirements by product line
✓ Assess current security documentation gaps
Phase 2: Infrastructure Development (Q3-Q4 2025)
✓ Implement Centralized Compliance Data Backbone linking security documentation to BOMs
✓ Deploy Supplier Self-Service Compliance Portals with CRA-specific questionnaires
✓ Establish Continuous Compliance Monitoring for vulnerability tracking
✓ Integrate security documentation with PLM and ERP systems
Phase 3: Supplier Engagement (Q1-Q2 2026)
✓ Collect security attestations from critical suppliers
✓ Validate supplier vulnerability disclosure procedures
✓ Establish incident response communication channels
✓ Verify supplier software update support commitments
Phase 4: Documentation Validation (Q3-Q4 2026)
✓ Complete technical documentation packages for Important Products
✓ Initiate conformity assessment with notified bodies
✓ Validate vulnerability management procedures through tabletop exercises
✓ Establish market surveillance response protocols
Phase 5: Continuous Operation (2027+)
✓ Maintain Continuous Audit-Ready Documentation through automated workflows
✓ Monitor regulatory updates through CORA-powered regulatory intelligence
✓ Generate incident reports within CRA timeline requirements
✓ Support customer security queries through Customer Trust Centers & Self-Service Reporting
Manufacturers managing multiple compliance obligations should explore how AI-powered compliance automation reduces preparation time and maintains compliance accuracy across regulatory frameworks.
What Tools Support End-to-End Product Compliance from Design Through Production and Shipment?
Manufacturers require compliance systems that integrate security documentation with product development workflows rather than treating cybersecurity as a post-production audit task. End-to-end product compliance systems must:
✓ Capture security requirements during design phase through Design-For-Compliance PLM Workflows
✓ Validate component security attestations during procurement
✓ Track vulnerability status during manufacturing
✓ Generate shipment-ready security documentation packages
✓ Maintain post-market surveillance records throughout product lifecycle
Certivo provides the Integrated PLM ERP Compliance Thread that connects security documentation with existing product data systems, enabling manufacturers to manage CRA compliance through existing operational workflows rather than parallel tracking systems.
Organizations should also review cybersecurity and digital compliance solutions that address broader digital product requirements beyond CRA-specific mandates.
Frequently Asked Questions
What solutions provide automated alerts when regulations affecting parts or SKUs change?
Certivo's Regulatory Intelligence & Horizon Scanning system monitors CRA updates and automatically correlates regulatory changes with affected SKUs. CORA generates alerts when new vulnerability disclosure requirements, conformity assessment procedures, or market surveillance guidance impacts specific product lines, enabling compliance teams to prioritize remediation activities based on regulatory urgency and SKU-level exposure.
What software helps monitor global regulatory updates and map them to specific SKUs?
CORA-driven compliance intelligence tracks cybersecurity regulations across jurisdictions and maps requirements to product portfolios based on BOM composition, target markets, and product classification. This enables manufacturers to maintain Multi Jurisdiction EHS & ESG Management for cybersecurity alongside existing materials compliance frameworks like REACH and RoHS, with automatic SKU-level mapping of regulatory obligations.
What tools support end-to-end product compliance from design through production and shipment?
Certivo provides the Integrated PLM ERP Compliance Thread that captures security requirements during design phase through Design-For-Compliance PLM Workflows, validates component security attestations during procurement, tracks vulnerability status during manufacturing, generates shipment-ready security documentation packages, and maintains post-market surveillance records throughout product lifecycle. This eliminates the need for parallel tracking systems outside core operational workflows.
What systems help manufacturers meet CRA's 24-hour incident reporting requirements?
Certivo automates vulnerability correlation through BOM-Level Material Mapping that links component identifiers to CVE databases and generates exposure reports within minutes of vulnerability publication. Continuous Compliance Monitoring infrastructure calculates affected SKUs, deployed product versions, and customer installations automatically, enabling manufacturers to meet the CRA's strict 24-hour reporting timeline for actively exploited vulnerabilities with pre-populated incident documentation.
How do manufacturers maintain CRA technical documentation for 5-10 year lifecycle periods?
Certivo's Continuous Audit-Ready Documentation infrastructure maintains version-controlled security records linked to specific SKUs and product generations. Digital Passports & Traceability IDs ensure technical documentation remains accessible throughout extended product lifecycles regardless of organizational changes, system migrations, or supplier transitions, while automated retention policies ensure compliance with CRA's long-term documentation requirements across product portfolios.
Conclusion
EU Cyber Resilience Act compliance represents a structural shift in how manufacturers manage product security, requiring Continuous Audit-Ready Documentation maintained throughout extended product lifecycles. Organizations relying on manual tracking systems face documentation gaps, supplier coordination delays, and vulnerability management bottlenecks that create market access risks as 2027 enforcement approaches.
Certivo automates EU Cyber Resilience Act compliance through BOM-Level Compliance Intelligence, Supplier Self-Service Compliance Portals, and CORA-powered regulatory intelligence that transforms cybersecurity documentation from reactive audit preparation into continuous operational readiness. This infrastructure positions manufacturers for compliance with CRA security requirements while maintaining existing materials and environmental compliance obligations through unified data management systems.
The organizations that establish Centralized Compliance Data Backbone infrastructure now will manage CRA compliance as a competitive advantage rather than operational burden. Those deferring preparation until enforcement deadlines face compressed implementation timelines that increase non-compliance risk and limit market access options.
Contact Certivo to assess your CRA compliance readiness and explore how AI-Native Compliance Automation accelerates cybersecurity documentation preparation while reducing operational overhead across global manufacturing operations.
Vasanth
Vasanth is a skilled Compliance Engineer with over five years of experience specializing in global environmental regulations, including REACH, RoHS, Proposition 65, POPs, TSCA, PFAS, CMRT, EMRT, FMD, and IMDS. With a strong academic foundation in Chemical Engineering from Anna University, he brings a deep technical understanding to compliance processes across complex product lines.
Vasanth excels in analyzing Bills of Materials (BOMs), evaluating supplier declarations, and ensuring regulatory conformity through meticulous review and risk assessment. He is highly proficient in supplier engagement, adept at interpreting material disclosures, and experienced in preparing customer-ready compliance documentation tailored to diverse global standards.
Known for his attention to detail, up-to-date regulatory knowledge, and proactive communication style, Vasanth plays a critical role in maintaining product compliance and advancing sustainability goals within fast-paced, globally integrated manufacturing environments.